Our second installment in the new Sensor Intel Series is a monthly update for July to the vulnerability targeting information for the first half of 2022 that we published in July. This intelligence is based on our analysis of logs from a globally distributed sensor network maintained by our partners Effluxio.
The most notable thing about July was that the IoT vulnerability CVE-2020-8958 surpassed CVE-2017-9841, after CVE-2017-9841 had held the top spot for the entire first half of 2022. The total traffic volume in July seeking CVE-2020-8958 was 8,244 connections, which not only exceeded July traffic targeting CVE-2017-9841 but was the largest amount of traffic targeting a single vulnerability we’ve seen in the entire seven-month period. We were unfortunately not able to discover a reason behind this spike in attention, but we do know that CVE-2020-8958 has been targeted at a significantly lower level throughout the entire period.
We also noted an increase in targeting diversity: whereas it initially appeared that only six vulnerabilities constituted 97% of the overall traffic for the original six-month overview, in July that same proportion of total traffic was spread over nine vulnerabilities (Figure 1). Furthermore, we also discovered traffic throughout the entire period targeting a few additional vulnerabilities (CVE-2021-28481 and CVE-2017-18368, as well as CVE-2020-8958) that had escaped our filters. Figure 1 data for January through June has been updated to reflect these additions.
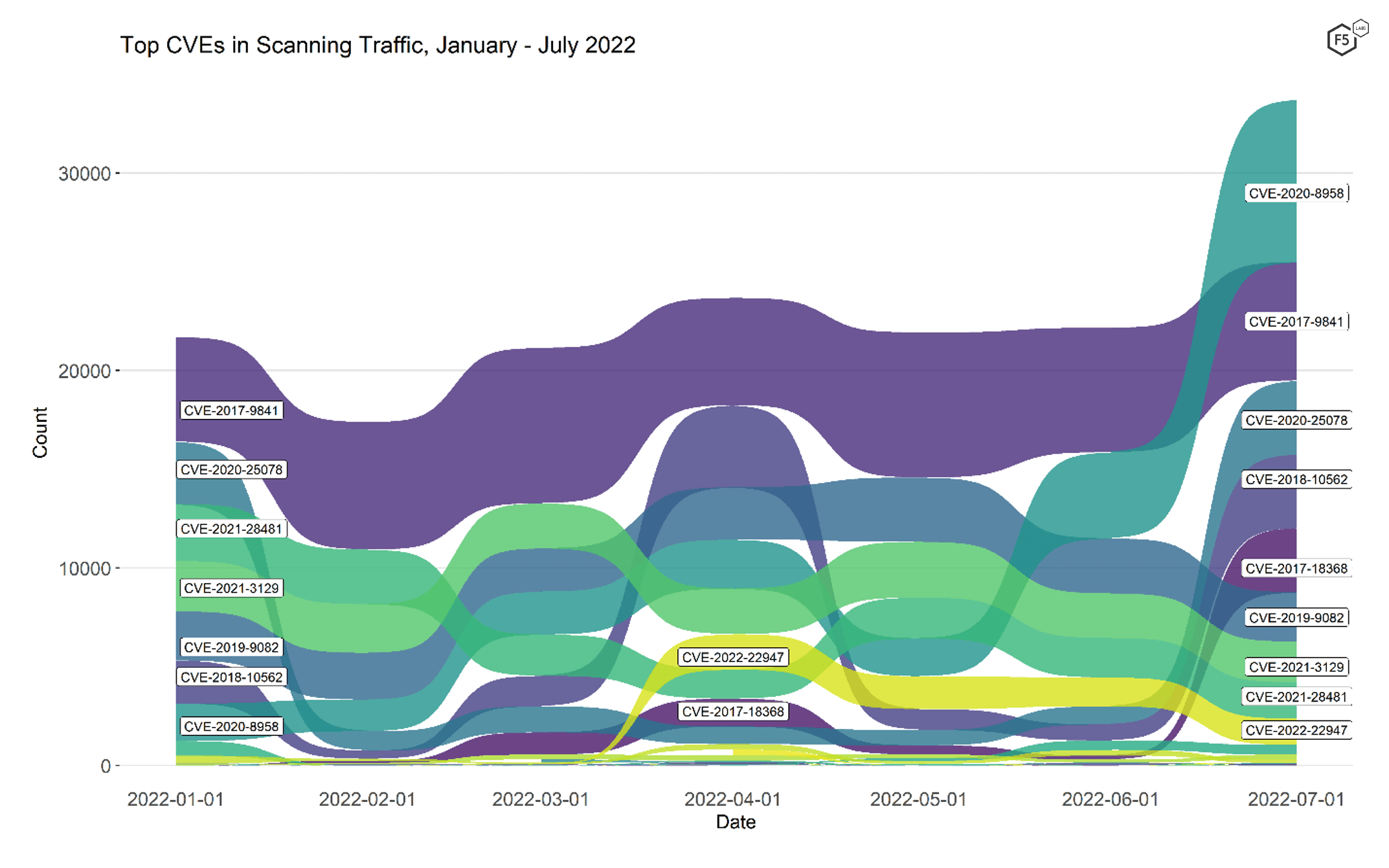
Figure 1. CVE targeting volume for 30 CVEs, January 2022 - July 2022. In July CVE-2017-9841 was surpassed in volume by another vulnerability for the first time since we started keeping track.
To get a better sense of the actual volume of traffic per vulnerability, Figure 2 shows the volume of July traffic targeting the top ten CVEs. This view emphasizes the dramatic growth in traffic targeting CVE-2020-8958 in July—it outstripped CVE-2017-9841 by more than a third.
Table 1 shows counts and monthly changes for all of the CVEs we identified in July traffic.
| CVE Number | Count | Change in Count (June – July) |
| CVE-2020-8958 | 8244 | 3876 |
| CVE-2017-9841 | 5991 | -303 |
| CVE-2020-25078 | 3739 | 2821 |
| CVE-2018-10562 | 3728 | 2915 |
| CVE-2017-18368 | 3265 | 3063 |
| CVE-2019-9082 | 2508 | -278 |
| CVE-2021-3129 | 2057 | -203 |
| CVE-2021-28481 | 1839 | -159 |
| CVE-2022-22947 | 1330 | -128 |
| CVE-2021-22986 | 447 | -7 |
| CVE-2021-41277 | 226 | 75 |
| CVE-2021-44228 | 198 | -92 |
| CVE-2022-1388 | 47 | 23 |
| CVE-2022-22965 | 19 | -5 |
| CVE-2020-9757 | 14 | 8 |
| CVE-2018-7600 | 13 | -7 |
| CVE-2020-28188 | 9 | 8 |
| CVE-2022-25369 | 9 | 8 |
| CVE-2008-6668 | 8 | 5 |
| CVE-2021-3577 | 8 | 2 |
| CVE-2018-7700 | 7 | -22 |
| CVE-2020-7796 | 6 | 3 |
| CVE-2021-33357 | 6 | 5 |
| CVE-2020-13167 | 5 | 4 |
| CVE-2020-3452 | 5 | -25 |
| CVE-2019-2767 | 4 | -1 |
| CVE-2021-29203 | 4 | 2 |
| CVE-2021-32172 | 3 | 0 |
| CVE-2018-1000600 | 2 | 1 |
| CVE-2021-21315 | 2 | 1 |
Table 1. Traffic counts for July and monthly change for CVEs. July was the first month in 2022 in which CVE-2017-9841 was not the top targeted CVE.
Other Observations
We have been filtering traffic strictly for CVEs because they are well-defined by the practitioner community and tend to have comparatively straightforward paths to remediation. However, the volume of traffic targeting more vague kinds of resources often surpasses any given CVE. Two of the most consistent targets tend to be scans or exploit attempts against Wordpress instances and phpMyAdmin instances.
Traffic targeting Wordpress instances in July make up 15,436 connections, which was nearly double that of the most popular CVE. Traffic targeting phpMyAdmin, which has a long history of vulnerabilities, outstripped any CVE nearly three times, with 24,772 connection attempts in July.1 While these kinds of targets are less clearly defined than CVEs and have more complicated mitigation requirements, they bear mention because of the sheer volume and focus that they receive from attackers. If you’re running a Wordpress or PMA site, your security posture deserves an extra look-over (or two).
CVE Writeups
Below you will find brief writeups and links to the National Vulnerability Database for all of the new CVEs that showed up in July. For CVEs that were present in the first six month dataset, see the first Sensor Intel Series article.
CVE-2020-8958
A command injection vulnerability in Guangshou 1GE ONU V2801RW 1.9.1-181203 through 2.9.0-181024 and in V2804RGW 1.9.1-181203 through 2.9.0-101024 which allowed remote attackers to execute arbitrary OS commands. The vast majority of these were simple requests to identify possibly vulnerable endpoints, but a few were attempting to log in with simple credential pairs (admin/admin, and the like). NVD
CVE-2017-18368
A critical command injection vulnerability in ZyXEL router model no. P660HN-T1A v1 TCLinux Fw $7.3.15.0 v001 / 3.40(ULM.0)b31. Traffic targeting this vulnerability in our logs was completely uniform, requesting exactly the same URI every time via a POST method with no body content. NVD
CVE-2021-28481
A critical remote code execution (RCE) vulnerability in Microsoft Exchange Server, unique from several other CVEs for Exchange that came out about a month earlier (CVE-2021-28480, CVE-2021-28482, CVE-2021-28483. The most common scan was done by scanners using the ‘Mozilla/5.0 zgrab/0.x’ User-Agent, which (assuming it isn’t being spoofed) is the User-Agent used by the zgrab scanner (part of Zmap). The rest used the User-Agent header associated with the Leakix internet scanning platform, although as that scanner is open source, they may not have been generated by that platform itself. NVD
CVE-2021-41277
A local file inclusion (LFI) vulnerability in Metabase, an open source data analytics platform, fixed in maintenance releases 0.40.5 and 1.40.5. This allowed attackers to view the contents of local files and environmental variables on the affected server. Our dataset shows that the vast majority of the attempts were trying to read /etc/hosts, and a handful went for /etc/passwd. Once again the User-Agent header was associated with the Leakix scanning platform. NVD
CVE-2021-22986
CVE-2021-22986 is critical unauthenticated remote command execution vulnerability on F5 BIG-IP versions 16.0.x before 16.0.1.1, 15.1.x before 15.1.2.1, 14.1.x before 14.1.4, 13.1.x before 13.1.3.6, and 12.1.x before 12.1.5.3 and BIG-IQ 7.1.0.x before 7.1.0.3 and 7.0.0.x before 7.0.0.2. In our dataset, a handful of these simply checked if a command could be run, but in most cases, an attempt was made to download a shell script from a remote server and execute it. NVD
CVE-2022-1388
CVE-2022-1388 is another critical vulnerability on F5 BIG-IP 16.1.x versions prior to 16.1.2.2, 15.1.x versions prior to 15.1.5.1, 14.1.x versions prior to 14.1.4.6, 13.1.x versions prior to 13.1.5, and all 12.1.x and 11.6.x versions. In our dataset, the majority of the time an actual attempt to exploit this was observed. NVD
July Port Scan Data
F5 Labs also analyzes data for TCP ports other than 80 and 443 from the Effluxio network. The top 10 ports for July 2022 follow patterns we’ve been seeing for years, with port 5900 (VNC) topping the list, followed by a collection of ports used mainly for remote access (ssh, telnet, ftp, RDP) and some database and mail related ports as well. Interestingly, despite decades of advice suggesting that SMB not be exposed to the internet, it still appears to be scanned for regularly.
| Port | % of total connections | Typical application |
| 5900 | 34.8% | VNC |
| 80 | 19.3% | HTTP |
| 22 | 10.8% | SSH |
| 23 | 10.2% | Telnet |
| 443 | 4.6% | HTTPS/TLS |
| 1080 | 2.8% | SOCKS proxy |
| 3389 | 2.5% | RDP |
| 3306 | 2.5% | Mysql/MariaDB |
| 25 | 1.6% | SMTP |
| 445 | 0.3% | SMB |
Conclusion
Last month we noted the unsurprising popularity of remote code execution vulnerabilities, but also recognized that two of the six vulnerabilities were IoT vulnerabilities. This month, not only is the top targeted CVE an IoT vulnerability, but several of the new vulnerabilities or newly prominent ones are as well, including CVE-2017-18368. In fact, 4 of the top 9 targeted vulnerabilities in July were IoT vulnerabilities. 2021 and 2022 have seen several record-breaking DDoS attacks, and we know how useful IoT devices are for DDoS attacks (/content/f5-labs-v2/en/labs/articles/threat-intelligence/the-hunt-for-iot--so-easy-to-compromise--children-are-doing-it.html).2 As a result we are left to speculate that threat actors are building infrastructure for future DDoS. Because of this, in addition to recommending vulnerability scanning and remediation, we also recommend scoping for DDoS protection and mitigation in one form or another.
Recommendations
- Scan your environment for vulnerabilities aggressively.
- Patch high-priority vulnerabilities (defined however suits you) as soon as feasible.
- Engage a DDoS mitigation service to prevent the impact of DDoS on your organization
- Use a WAF or similar tool to detect and stop web exploits.
- Monitor anomalous outbound traffic to detect devices in your environment that are participating in DDoS attacks.