Welcome to the dedicated Executive Summary for our 2023 Identity Threat Report. Here we've brought together the bullet-list style summary that opens the full report, as well as a few curated selections and charts to get immediately to the "what do I need to know" of it all.
And of course, if you want to dive into the details and the "why" and "how" behind today's threats to identity, you can jump over to the full report, or download the PDF (https://www.f5.com/labs/articles/threat-intelligence/2023-identity-threat-report-the-unpatchables). Both of them are one click away - we hate walling off content as much as you hate giving fake info just to read a report.
Executive Summary
- Threats to digital identities are continuous in nature, widespread in targeting, and progressive in their evolution.
- The average proportion of credential stuffing in unmitigated traffic for sampled organizations across all sectors was 19.4%.
- Post-mitigation, the average rate of credential stuffing was 6.0%.
- Mobile endpoints generally see higher rates of automation pre-mitigation than web endpoints.
- Travel, telecommunications, and technology firms experienced higher credential stuffing rates than other sectors.
- While authentication endpoints see higher traffic and automation rates than account management endpoints, account management endpoints serve critical roles for attackers, such as the creation of canary accounts and facilitation attacks for information gain.
- 65% of credential stuffing traffic was composed of unsophisticated HTTP requests with no browser or user emulation.
- Around 20% of malicious automation traffic on authentication endpoints was sophisticated, in that it successfully emulated human behavior on a real browser, including mouse movements and keystrokes.
- Aggregators, which play a significant role in several industries such as finance, can be both a source of noise in terms of detecting malicious automation, as well as a vector in their own right for attackers.
- Many organizations use authentication success rate to identify unwanted automation, but aggregator and canary account traffic can make authentication success rate metrics unreliable.
- The phishing industry has matured, with phishing kits and services driving down the requisite technical expertise and cost.
- Phishing appears to target financial organizations and large-scale/federated identity providers such as Microsoft, Facebook, Google, and Apple the most.
- Reverse phishing proxies, also known as real-time phishing proxies or man-in-the-middle (MITM) phishing, have become the standard approach. These proxies can harvest session cookies and defeat most multi-factor authentication (MFA).
- Detection evasion tools that defeat capabilities such as Google Safe Browsing are also a high priority for phishing.
- Multi-factor authentication bypass techniques have become more common, with successful strategies based on malware, phishing, and other social engineering vectors observed.
- Multi-factor authentication technologies based on public key cryptography (such as the FIDO2 suite of protocols) are significantly more resistant to observed MFA bypass techniques.
Credential Stuffing
Credential stuffing is a numbers game. It hinges on the fact that people reuse passwords, but the likelihood that any single publicly compromised password will work on another single web property is still small. Making credential stuffing profitable is all about maximizing the number of attempts, and that means it is also all about automation.
Prevalence
Quantifying the prevalence of credential stuffing across multiple different organizations is difficult because credential stuffing attacks against a single organization often occur in intense waves, then subside to a lower baseline level for some time. With that said, Figure 1 shows the daily mean proportion (with 95% confidence interval) of malicious automated traffic against the authentication surfaces of 159 customers.
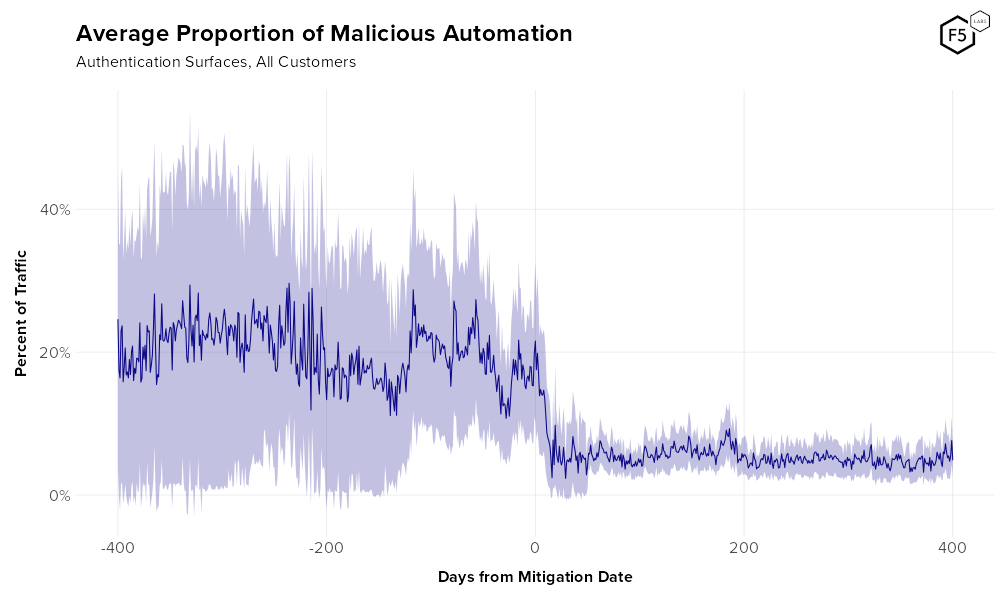
Figure 1. Average rate of malicious automation against authentication over time for all customers. Pale purple denotes a 95% confidence interval. Note the dramatic change in traffic upon mitigation.
On average one in five authentication requests comes from malicious automated systems, i.e., credential stuffing bots.
Of course, identity-related attacks aren't exclusive to authentication surfaces - in the full report we go much more in depth on different endpoints, as well as comparing platforms and industries.
Want to hear about attackers' tactics, techniques, and procedures? Yep, we cover that as well (canary accounts are especially useful for attackers), but here's a small nugget:
For unmitigated authentication endpoints, basic, low-sophistication attacks made up 65% of malicious traffic.
We also spent a fair amount of time looking into the lifecycle of all these compromised credentials. That's not new for us, of course, but by performing some overlap analysis between known compromised credentials and recently submitted credentials, we were able to come to some surprising conclusions. For one thing, even though we know about a lot of breaches and the creds harvested from them, that only accounts for about a quarter of the credentials that bots are using.
Three quarters of the stolen credential supply chain is unaccounted for.
Phishing
It goes without saying that detecting phishing is difficult, because most of the point of phishing is to be difficult to detect. We recently spoke to a security operations employee responsible for managing a commercial, off-the-shelf email phishing filter who said that their tool has a 95% false positive rate for phishing mails. This means that phishing costs everybody whether they fall for one or not.
We can see which organizations are the most phished by looking at the Anti-Phishing Working Group's data...
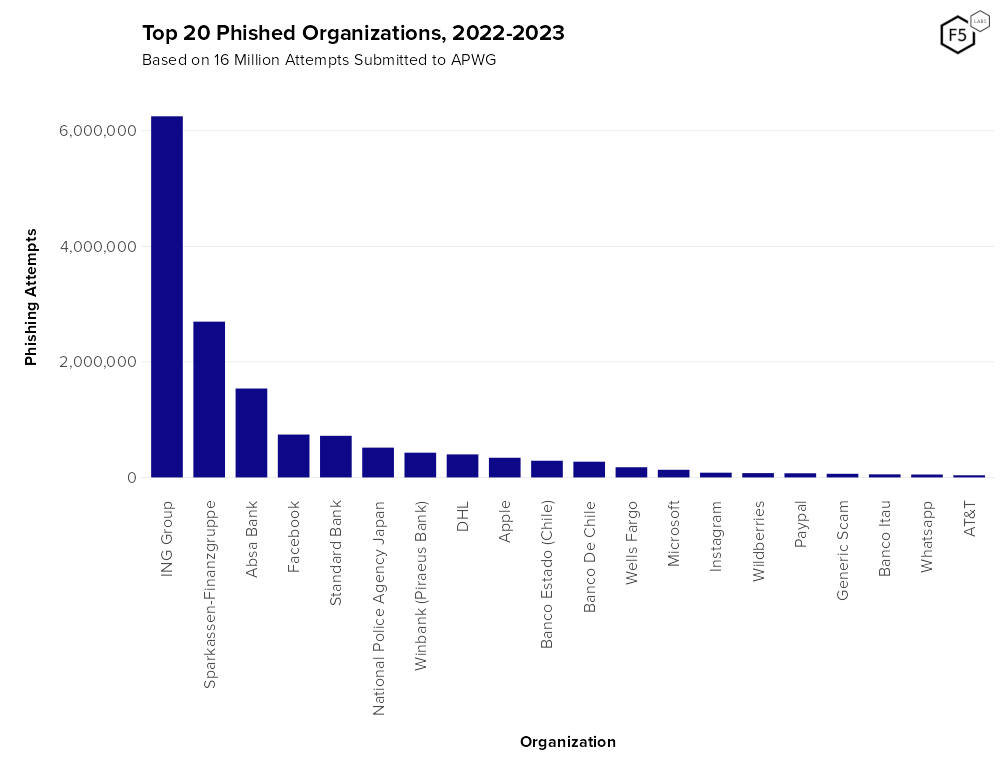
Figure 25. Top 20 phishing targets 2022-2023, per the Anti-Phishing Working Group. Financial organizations made up four of the top ten and ten of the top 20 (counting PayPal). Google is notably absent, although this could be due to selection bias.
... but to know where attackers want to be, you have to dig into their wish lists on the dark web. Which we did.
- Google
- Office 365
- Steam
- Yahoo
- WordPress
- Facebook
- iCloud
- Binance
- Amazon
- Dropbox
- Twitter
- Yandex.ru
- American Express
- Venmo
- GitHub
- Airbnb
- Namecheap
- Okta
Want to get into the weeds on phishing TTPs? Yep, that's in the report too.
Multi-factor Authentication Bypass
For more than a decade, the information security community has touted multi-factor authentication as a way to control identity risk. So of course attackers have been hammering away, and have found a handful of ways to bypass MFA. Phishing reverse proxies, malware, social engineering, and more - while having MFA is still much better than not having it, we are well past the point where you can set up an MFA protocol and call it good.
Over in the full report, we don't just talk about problems; we've got a whole stack of recommendations to mitigate these various identity threats. And because F5 Labs’ mission is to deliver threat intelligence, not to promote products, all of our recommendations are vendor-agnostic, and instead give you practical steps to protect your environment and your customers.