Report
Encryption
The State of Post-Quantum Cryptography (PQC) on the Web
We analyze the world’s most popular websites and most widely used web browsers to determine the current state of PQC adoption on the web.
Report
Bots and Automated Attacks
2025 Advanced Persistent Bots Report
Uncovering the true scale of persistent bot activity, and the advanced techniques that bot operators use in order to remain hidden from bot defenses.
Report
DDoS
2024 DDoS Attack Trends
Unveiling the rise of Hacktivism in a tense global climate.
Report
Threat Detection
2023 Identity Threat Report: The Unpatchables
We are excited to announce a new report covering threats to digital identities. This report goes into detail on credential stuffing, phishing, and multifactor authentication bypass techniques.
Latest Research
AI
Topic Bridge
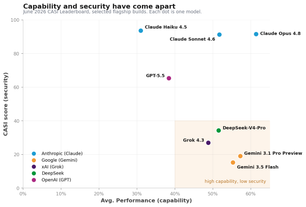
CASI leaderboard shifts, and two incidents where AI was handed the keys.
What is Threat Research?
For F5 Labs, threat research is a broad endeavor. It includes analyzing vulnerabilities and their impacts, attacker trend data, malware investigation, development of open source tools to identify attacks and mitigate exposure, industry and regional assessments, and consideration of a wide range of attacker tactics and techniques. The attack surface is always expanding, which means attackers are always finding new vulnerabilities to exploit and defenders are always having to develop new ways to stop them.
Apache Parquet
Canary Exploit Tool for CVE-2025-30065 Apache Parquet Avro Vulnerability
Investigating a schema parsing concern in the parquet-avro module of Apache Parquet Java.
Sensor Intel Series
Sensor Intel Series
Analyzing the Global Increase in Vulnerability Scanning in 2024
BotPoke comes to the foreground yet again.
What Are the Risks You Need to Worry About?
This is a complex question. One way to think about it is to consider what attackers are doing: a zero-day vulnerability is always concerning, but if it's not being exploited, it's as noisy as a tree in the forest when no one's around. That's why we look at real world attack data to see what vulnerabilities are being actively targeted, what malware campaigns are gaining steam, and what differences we see between different industries and regions.
What Should I Do to Protect My Environment?
Another way to think about your exposure to threats is to consider what risks are specific to your ecosystem. A high-profile banking trojan campaign is much less concerning to industrial manufacturers, and you only need to patch a vulnerability with a 10.0 CVSS if you're using the affected system. From this perspective, it's often useful to consider types of attacks and gauge how likely it is that they'll affect your ecosystem, then consider whether there's straightforward actions you can take or best practices you can implement to reduce your risk. When we conduct research, we always conclude by giving you some guidance on what to do next.
Bots and Automated Attacks
2025 Advanced Persistent Bot Report: Scraper Bots Deep-Dive
How much do scraper bots affect your industry?
Ready to Learn More?
Threat research is at the core of what F5 Labs does. We are security practitioners with decades of experience, so we know how important it is to cut out the fluff and stay focused on the data. We try to balance keeping up with emerging trends like post-quantum cryptography with a steady hand on security fundamentals (because it's still always DNS), all with a view towards trying to help you solve problems. Below, you can find a collection of all of our threat research.